Ubuntu Infrastructure Down for Over a Day After Sustained DDoS Attack
The Ubuntu infrastructure down crisis has stretched into its second day, leaving users, sysadmins, and developers across the globe scrambling for answers. Servers belonging to Ubuntu and its parent company Canonical were knocked offline early Thursday and have remained largely inaccessible ever since. The timing couldn’t be worse, as the outage is preventing the company from communicating critical security information following the troubled disclosure of a major Linux vulnerability.
For an open-source giant that powers an enormous chunk of the world’s servers, cloud workloads, and developer environments, this kind of disruption is more than an inconvenience. It’s a serious operational and security concern.
What Users Are Experiencing
Over the past 24-plus hours, attempts to reach Ubuntu and Canonical websites or pull operating system updates directly from Ubuntu servers have consistently failed. The good news, if there is any, is that mirror sites have continued to operate normally, allowing users to still access updates through alternate channels.
Canonical’s official status page acknowledged the situation, noting that the company’s web infrastructure is under a sustained, cross-border attack and that teams are actively working on a resolution. Beyond that brief statement, both Ubuntu and Canonical officials have remained largely silent since the outage began.
Pro-Iran Group Claims Responsibility
The disruption is reportedly the work of a group sympathetic to the Iranian government, which has publicly claimed responsibility through posts on Telegram and other social media platforms. According to those claims, the group used a DDoS-for-hire service called Beam to overwhelm Canonical’s servers with traffic.
While such tools are often advertised as legitimate “stress-testing” platforms designed to evaluate how websites perform under heavy load, in practice they function as paid weapons used to take down third-party sites. The same group has reportedly been linked to recent DDoS incidents targeting eBay as well.
These so-called stressor or booter services have plagued the internet for decades, slipping in and out of legal gray zones despite repeated international crackdowns.
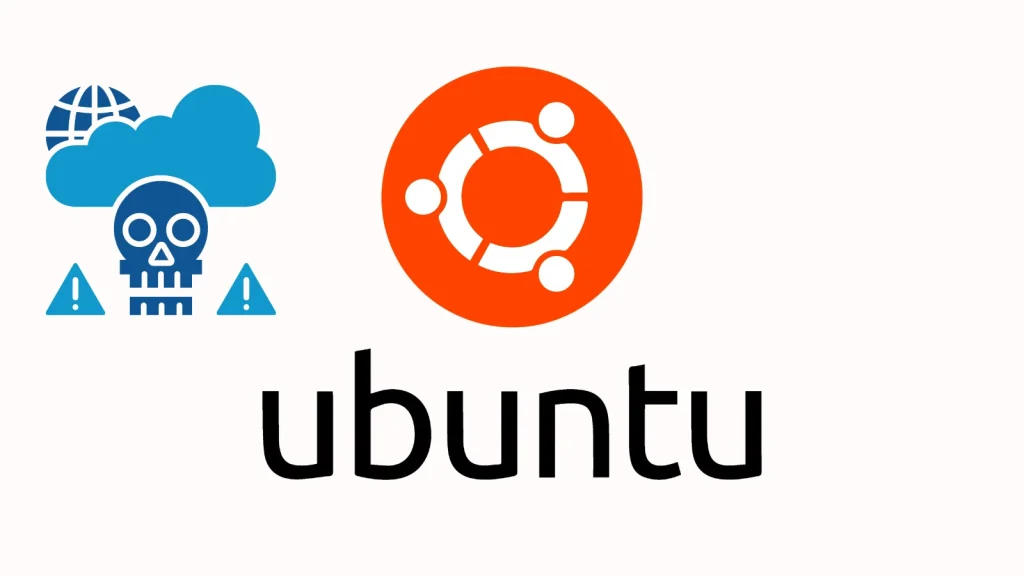
A Long List of Affected Domains
According to a moderator on AskUbuntu.com, a wide range of Ubuntu and Canonical web properties have been hit hard. Among the URLs that remained inaccessible during the outage were:
- security.ubuntu.com
- archive.ubuntu.com
- ubuntu.com
- canonical.com
- portal.canonical.com
- blog.ubuntu.com
- developer.ubuntu.com
- assets.ubuntu.com
- academy.canonical.com
- jaas.ai
- maas.io
- The Ubuntu Security API for CVEs
- The Ubuntu Security API for Notices
The breadth of affected domains shows just how deeply the attack has cut into Canonical’s online presence, taking out everything from the main marketing site to its critical security-related infrastructure.
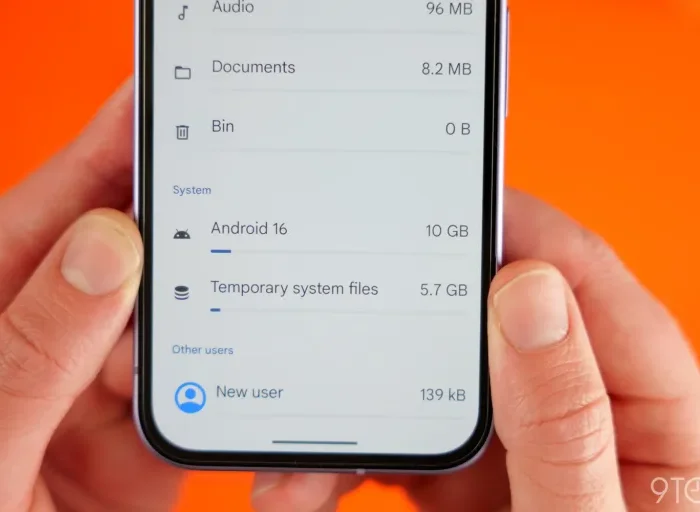
Bad Timing for a Major Linux Vulnerability
The outage couldn’t have struck at a more sensitive moment. Just hours before Ubuntu’s services went dark, security researchers released proof-of-concept exploit code for a serious flaw affecting nearly all Linux distributions, including Ubuntu.
The vulnerability allows untrusted users in data centers, universities, shared hosting environments, and other multi-user settings to gain full root control of affected systems. That level of access is essentially unrestricted, giving attackers the ability to:
- Modify or delete any file on the system
- Install or remove any software
- Steal sensitive credentials and certificates
- Pivot to other machines in the network
- Persist undetected through reboots and updates
When such a critical bug surfaces, fast and reliable communication from the OS vendor is essential. Unfortunately, with Ubuntu’s primary infrastructure offline, distributing official guidance and patches has become significantly more difficult.
Mirrors Are Helping, but Communication Is Crippled
There is a small silver lining. Ubuntu’s mirror network — independently hosted servers that distribute software packages and updates — has remained largely unaffected. Users in need of urgent security patches can still pull updates from those mirrors and continue to maintain their systems.
However, the mirrors are limited in scope. They handle software distribution, not communication. That means while users can technically install fixes, they’re left guessing about official advisories, severity ratings, and detailed mitigation guidance — all of which traditionally come from Ubuntu’s own security pages and APIs.
For sysadmins managing large fleets of servers, this gap is more than just frustrating. It complicates incident response, slows down patch prioritization, and creates uncertainty during what should be a coordinated security response.
Why Booter Services Continue to Thrive
The persistence of stressor and booter services is a long-running issue in cybersecurity. Despite multiple international law enforcement operations targeting these platforms, new ones routinely pop up to replace those that get shut down. Their continued availability empowers anyone — from politically motivated groups to bored teenagers — to launch significant attacks for relatively small fees.
Several reasons explain why these platforms keep returning, including:
- Cheap entry points often costing only a few dollars per attack
- Use of cryptocurrency for hard-to-trace payments
- Hosting in countries with limited cooperation with global authorities
- Constantly evolving tactics that bypass standard mitigations
- A wide pool of vulnerable, hijacked devices that can be weaponized
This ecosystem fuels the kind of disruption Ubuntu and Canonical are now facing, and it’s a reminder that even widely used, well-funded platforms aren’t immune to opportunistic attacks.
Lingering Questions About the Long Outage
One of the more puzzling aspects of the situation is just how long Ubuntu’s infrastructure has remained offline. The cybersecurity industry offers a wide variety of DDoS protection solutions, including some free-tier services from major providers, that should be able to absorb attacks of this nature.
Whether Canonical is dealing with a particularly large-scale assault, internal complications, or a combination of both, the extended downtime has raised concerns about resilience and incident handling at one of the most influential open-source organizations in the world.
For now, the company has not publicly explained the technical details behind the prolonged outage or offered a timeline for full restoration.
What This Means for the Linux Community
The Ubuntu infrastructure down event highlights several important realities for the broader Linux ecosystem:
- Even established open-source giants are vulnerable to modern cyber threats
- Communication channels are just as critical as software distribution
- The reliance on a centralized website to handle security updates is a single point of failure
- Mirror networks are valuable but cannot fully replace official guidance
- DDoS attacks remain a persistent and disruptive threat
For Ubuntu users, the practical advice for the moment is simple: keep an eye on trusted mirror sources for updates, follow reliable security news channels for guidance, and stay alert to news about the unfolding Linux vulnerability.
As Canonical works to restore its systems, the broader takeaway is clear. Even in 2026, the basic but devastating impact of a coordinated DDoS attack can ripple through infrastructure used by millions, reminding the tech world that resilience must always remain a top priority.
Author
-
Lucienne Albrecht is Luxe Chronicle’s wealth and lifestyle editor, celebrated for her elegant perspective on finance, legacy, and global luxury culture. With a flair for blending sophistication with insight, she brings a distinctly feminine voice to the world of high society and wealth.